Encrypted apps
Put banking, social, and work apps behind encryption. Toggle protection on and choose which titles live inside the vault.
Privacy · Control · Clarity
CryptoBox is a premium privacy utility that locks sensitive apps and photos behind smart rules, gives you honest usage insights, and reacts the moment you need to disappear from the screen.

Product pillars
One place to hide apps, protect albums, understand screen time, and arm passive defenses—without sacrificing a premium, calm interface.
Put banking, social, and work apps behind encryption. Toggle protection on and choose which titles live inside the vault.
Keep personal media in an encrypted album with optional QR-based encryption flows for extra peace of mind when sharing access.
See today’s usage, how many apps you touched, and a clear breakdown of where your attention went—so you can act, not guess.
Tie visibility to places that matter—office campuses, co-working spaces, or home—so protection follows your day automatically.
Set windows like evenings or focus hours when selected apps stay hidden or locked, aligned with how you already plan your time.
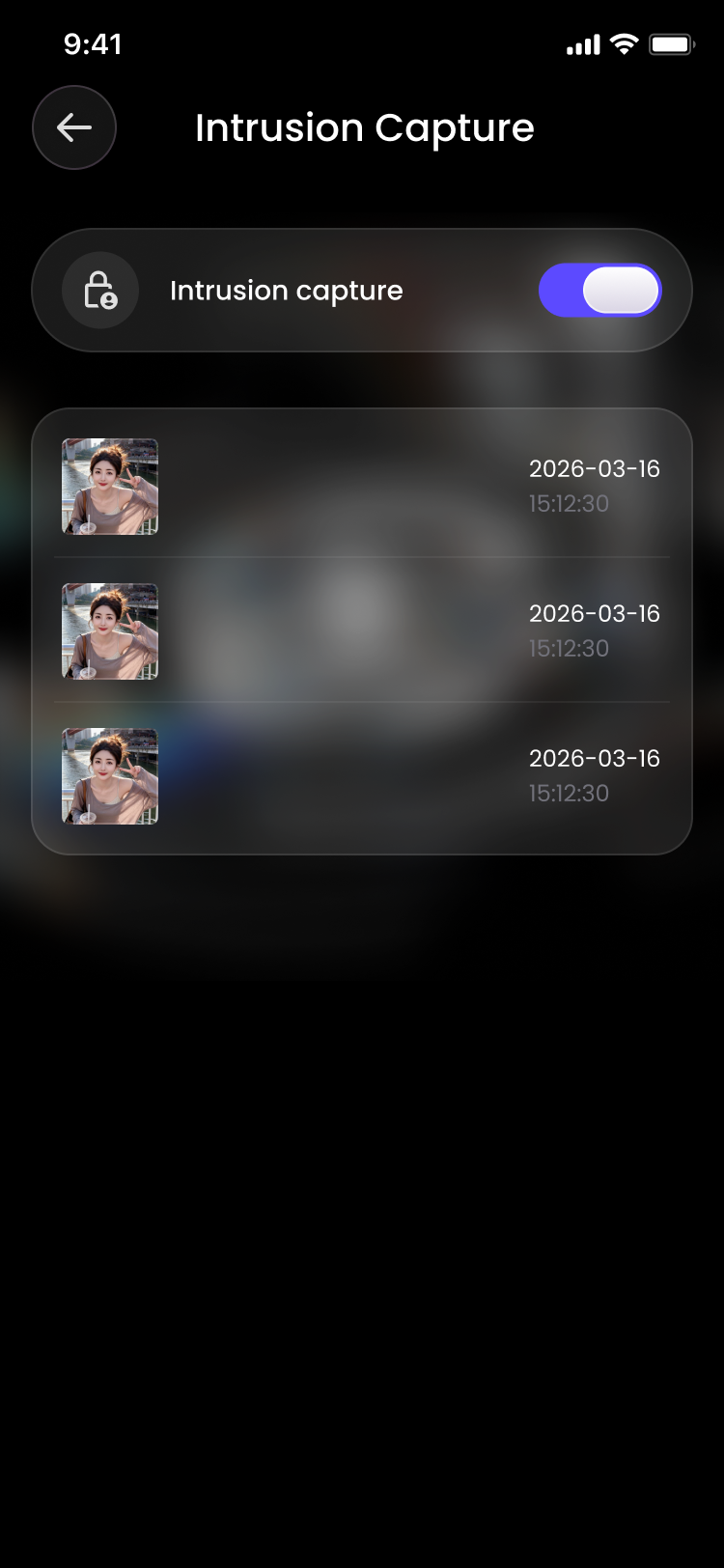
Wrong-password capture helps you spot unauthorized attempts with timestamped evidence—so you know what happened, not just that something failed.
Privacy on autopilot
CryptoBox doesn’t ask you to micromanage every tap. Combine time ranges and locations so sensitive surfaces only appear when the context is right.
A single glass card shows which apps are protected, whether the vault is on, and the schedules or locations that activate it—like evening focus blocks or a named campus zone.

Move personal shots into a gradient vault. Add new items safely and use QR encryption when you need a stricter hand-off than a simple folder.

Usage intelligence
The dashboard opens with the numbers that matter: total screen time today, how many apps you actually launched, and a horizontal trail of the heaviest hitters—from messaging to mail to notes.

Stealth & response
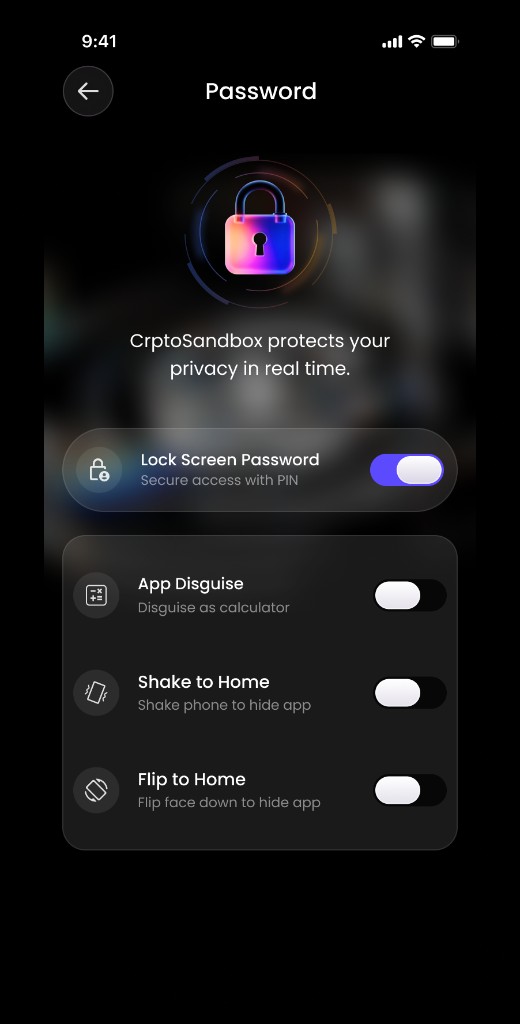
Beyond vaults, CryptoBox ships with real-time protections: PIN entry, calculator disguise, shake-to-home, and flip-to-home—so you can exit sensitive views before they become a liability.
Intrusion capture
Enable capture on wrong password to record intrusion attempts. Review a chronological log with timestamps so you can reconcile access with what actually happened on the device.
By the numbers
Questions
Install from your preferred store when available, or sideload the build your team distributes. Same glass UI. Same sandbox mindset.